Kronos malware was first discovered around June 2014, by a Russian Security researcher named VinnyK written malware scripts in Russian language and later translated into English.
Twitter: https://twitter.com/x0rz/status/893191612662153216
Kronos malware was initially available for sale from Russian underground forum with a price tag of $7000, as this malware multiple modules for different evading and detecting techniques. It also used for the purpose of the downloading other malware. One such email campaign occurred in Banking trojans to continue; Kronos acted as a loader with a new Point-Of-Sale (POS) malwares.
It was initially targeted UK and North America. And the email messages contained a document attachment and malicious link which attacker had control over the suspicious domain.

Link contained URL: hxxp://intranet[.]excelsharepoint[.]com/profile/Employee[.]php?id= [base64 encoded e-mail address]
Kronos Malware elements to be noted as,
- Malware to CnC communication encryption.
- Sanboxing bypassing.
- Antivirus bypassing.
- Defending from other trojans with user mode 32bit and 64bit rootkit.
- User Common credential-stealing techniques such as form grabbing and HTML injections from major browser like IE, Firefox and Chrome.
- Consistently targets the financial departments like Banking, Payroll etc.,
Kronos malware detections
The malware uses an undetected injection method which bypasses the proactive anti-Virus solutions. And the communication is encrypted between the bot and panel against the sniffers.
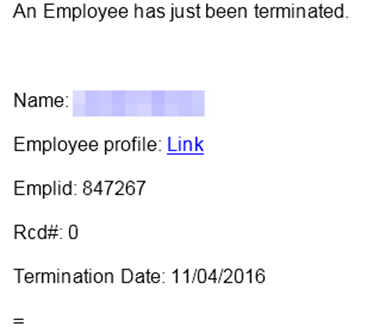
In 2021, almost near to the Christmas Eve the Kronos Malware has again crippled targeting the HR (Human Resource) provider UKG. And it also unfortunate that the employees/Customers may miss the payroll for this week. Still the UKG is investigating the attack, so meanwhile it is better to block the initial few IOCs listed and implement proper security controls to stop spreading such attacks.
Few of the Indicators of Compromise (IOC) to monitor,
Path:
Kronos malware install in the path: (%APPDATA%/Microsoft/[machine-specific GUID]): and persistence is achieved with the help of a simple Run key in the registry.
Suspicious URL:
hxxp://invoice.docs-sharepoint[.]com/profile/profile[.]php?id=[base64 e-mail address]
hxxp://invoice.docs-sharepoint[.]com/profile/download[.]php
hxxps://feed.networksupdates[.]com/feed/webfeed.xml
add.souloventure[.]org Domain RIG-v domain
hxxp://intranet.excelsharepoint[.]com/profile/Employee[.]php?id=[base64 e-mail address]
hxxp://info.docs-sharepoint[.]com/officeup[.]exe
hxxp://www.networkupdate[.]club/kbps/connect[.]php
hxxp://networkupdate[.]online/kbps/upload/c1c06f7d[.]exe
hxxp://networkupdate[.]online/kbps/upload/1f80ff71[.]exe
hxxp://networkupdate[.]online/kbps/upload/a8b05325[.]exe
hxxp://invoicesharepoint[.]com/gateway[.]php
hxxp://webfeed.updatesnetwork[.]com/feedweb/feed[.]php
hxxp://intranet.excel-sharepoint[.]com/doc/employee[.]php?id=[base64 e-mail address]
hxxp://profile.excel-sharepoint[.]com/doc/office[.]exe
http://springalove.at:80/noix/connect.php
http://springahate.at:80/noix/connect.php
Hash Values:
4b5f4dbd93100bb7b87920f2f3066782a8449eb9e236efc02afe570c1ce70cf5
90063c40cb94277f39ca1b3818b36b4fa41b3a3091d42dfc21586ad1c461daa0
711431204071b1e6f5b5644e0f0b23464c6ef5c254d7a40c4e6fe7c8782cd55c
4ba3913d945a16c099f5796fdeef2fda5c6c2e60cb53d46a1bfae82808075d74
a78b93a11ce649be3ca91812769f95a40de9d78e97a627366917c4fcd747f156
e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855
d0caf097ea0350dc92277aed73b0f44986d7d85b06d1d17b424dc172ce35a984
d9d1f02c8c4beee49f81093ea8162ce6adf405640ccacd5f03ce6c45e700ee98
093c81f0b234c2aa0363129fdaaaf57551f161915da3d23f43a792b5f3024c1e
fd5412a7c71958ecdffa7064bf03c5f1931e561a1e71bc939551d5afb8bf7462
269f88cfa9e9e26f3761aedee5d0836b5b82f346128fe03da28a331f80a5fba3
Command and Control (CnC)
46.175.146.50
46.172.209.210
47.188.161.114
74.109.250.65
77.122.51.88
77.122.51.88
89.25.31.94
89.185.15.235
91.196.93.112
176.32.5.207
188.25.234.208
109.121.227.191
IDS/IPS Coverage
2018125 ET CURRENT_EVENTS SUSPICIOUS .PIF File Inside of Zip
2020077 ET TROJAN Kronos Checkin M2
2020080 ET TROJAN Kronos Checkin
2022124 ET TROJAN Win32.Sharik Microsoft Connectivity Check
2022550 ET CURRENT_EVENTS Possible Malicious Macro DL EXE Feb 2016
2023196 ET CURRENT_EVENTS RIG EK Landing Sep 12 2016 T2
2023401 ET CURRENT_EVENTS RIG EK URI struct Oct 24 2016 (RIG-v)
2816808 ETPRO CURRENT_EVENTS RIG EK Flash Exploit Mar 29 2016
2823254 ETPRO TROJAN ScanPOS Exfiltrating CC Data
2823288 ETPRO TROJAN Zeus Variant CnC SSL Cert
Conclusions:
Today world ransomware attacks are increasing more and it is critical to take proper backup of the important data and implement security controls and Security user awareness to the users. Work with BCP to have contingency plans in the case of the cyber attacks in the Organizations. And receive latest updates of the breached vendor from here.
Reference:
https://www.proofpoint.com/us/threat-insight/post/kronos-reborn
