Cybersecurity researchers have discovered a new malware evasion technique called “Process Ghosting” with a new executable image tampering attack which could be potentially abused by the hackers in the windows environment. The attacker can write the malware to the disk in a way that it’s difficult to scan or delete the file, here deleted malware gets executed from the disk as if it was a regular malware file.
Whereas, this process ghosting technique does not involve any code injection, process hollowing, or Transactional NTFS (T*F). And the attack seems similar to Doppelgänging and Herpaderping which abuse the behaviour to evade the security product that creates a gap between the processes created and it has tampered with the backing executable before the execution is being notified by the security scan detections.
What is Process Doppelgänging?
Here the adversary may inject malicious code into the process via process Doppelgänging to evade the security controls and elevated privileges. The method of executing arbitrary code in the address space of the live process is known as Process Doppelgänging.
Process Doppelgänging can be executed in 4 steps as,
- Transact – Create a (TxF) transaction using a legitimate executable then overwrite the file with malicious code. And these changes will be isolated and only visible within the context of the transaction.
- Load – Create a shared section of memory and load the malicious executable.
- Rollback – Reverse the changes to the original executable that effectively removes the malicious code from the file system.
- Animate – Create a process from the affected section of memory and initiate execution of a process.
What is process herpaderping?
It is an attacking technique in which the digital adversaries modify the contents on-disk once after the image mapping is done to execute the process. This type of process can confuse and evade the security products and Operating systems and even may allow the malicious programs with this process herpaderping.
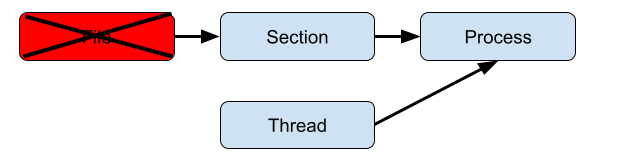
Process herpaderping can be executed as,
- Write target binary to disk, keeping the handle open. This is what will execute in memory.
- Map the file as an image section (NtCreateSection, SEC_IMAGE).
- Create the process object using the section handle (NtCreateProcessEx).
- Using the same target filehandle, obscure the file on disk.
- Create the initial thread in the process (NtCreateThreadEx). At this point, the process creation callback in the kernel will fire. The contents on the disk do not match what was mapped. Inspection of the file at this point will result in incorrect attribution.
- Closing the handle. IRP_MJ_CLEANUP will occur here.
Technical analysis of Process ghosting technique
As per the researchers, the ghosting process can be built upon Doppelgänging and Herpaderping to run the executables that have already deleted the malware files from the disk. It includes several ways to delete files in windows,
- Create a new file over the old one with the FILE_SUPERSEDE or CREATE_ALWAYS flags set.
- Set the FILE_DELETE_ON_CLOSE or FILE_FLAG_DELETE_ON_CLOSE flags when creating or opening the file.
- Set the DeleteFile field in the FILE_DISPOSITION_INFORMATION structure to TRUE when invoking the FileDispositionInformation file information class via NtSetInformationFile.
Here, the delete restriction is effective once the executable file is mapped into the image section, and then creates a file and mark it for deletion, map in the image section, close the file to complete the deletion process, and then creates processes from the non-fileless section. This technique is called Process ghosting.
We can understand more from the attack flow of process ghosting,
- Create a file
- Put the file into a delete-pending state using NtSetInformationFile(FileDispositionInformation). Note: Attempting to use FILE_DELETE_ON_CLOSE instead will not delete the file.
- Writing the payload executable to the file. The file is already delete-pending. The delete-pending state also blocks external file-open attempts from the system.
- Create an image section for the file.
- Close the delete-pending handle, deleting the file.
- Create a process using the image section.
- Assign process arguments and environment variables.
- Creates a thread to execute in the process.
Upon the thread creation, the antivirus callbacks are involved which will occur after the deletion of the file. And attempts to open the file or perform I/O on the deleted file with status STATUS_FILE_DELETED. When trying to open the file before the deletion is completed will get an error with STATUS_DELETE_PENDING. This type of tampering can be applied to DLLs as well, as they are directly mapped to the image sections.
During the demo, researchers observed that windows defender initially attempting to open the payload for scanning, but the process is not succeeded as the file is in a delete-pending-state. The defender tries again to scan the file but by the time file is deleted from the system to successfully execute the malware from the deleted file like a “Ghost” without any issues.
Detection of the Process ghost malware
Security researcher Gabriel Landau used Elastic search to detect the process of Image tampering techniques which includes Ghosting, Doppelgänging, and Herpaderping. It detects the abnormalities of the file by checking the FILE_OBJECT during the creation callback process. And the reported process creates the events under process.Ext.defense_evasions.
Comparison of various tampering techniques
We can create basic API workflow techniques across Ghosting, Doppelgänging, and Herpaderping as,
Ghosting Technique: delete pending -> write -> map -> close (delete) -> execute
Hollowing Technique: map -> modify section -> execute.
Doppelgänging Technique: transact -> write -> map -> rollback -> execute.
Herpaderping Technique: write -> map -> modify -> execute -> close.
