Recently security researchers have brought to a notice that an Android malware that pretends to be the legitimate ARMAAN (armaan.apk) application which would be developed by India’s govt related to the Indian Army has malware in it. The ARMAAN (Army Mobile Aadhaar App Network) is an application that covers various facts of information and services related to all Indian Army and it’s used by only Indian Army personnel. And this can be used by serving Indian Army personnel.
Security Researchers in the recent Twitter post found that the threat actors have customized the legitimate ARMAAN app and added malicious code in the app. And from the analysis, the malware researchers have observed that malware uses the icon, name, and Source code of the Android app ARMAAN to perform RAT activities.
Upon successful exploitation, the malicious application could steal sensitive information such as contacts, SMS logs, call logs, location, files from external storage, etc., from the victims’ devices.
Technical Analysis of the Malware
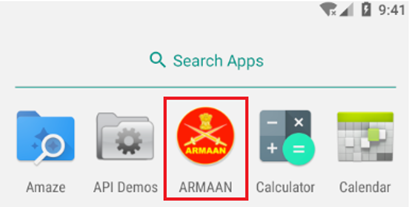
The android app named ARMAAN app (ARMAAN.apk) installs in the victim’s Android device as displayed below,
Once the successful installation, the malware requests for Aadhar number of the personnel, which is again feature of legitimate ARMAAN application. Where the user inputs the requested Aadhar number, the malware communicates with the official ARMAAN server to verify the account.
And researchers have also found that the modified legitimate ARMAAN app had an additional package of TAs added by the attackers which containing malicious codes.
Few commands used by TA to control the infected devices.
D%r6t* – Get SMS data
s%7n@2 – Get Contacts data
i*g4#3 – Get Call logs data
O@y7J& – Start mic recording
5w$I!7 – Get document files
1^R$4t – Get images from the WhatsApp folder
j*7e@4 – Click photos from the device camera.
Conclusions
As per the security researchers, the malicious app poses a serious threat to the Indian Armed forces. It can perform Remote Access Trojan (RAT) malware activities to steal sensitive data of Indian Personnel’s which includes contacts, SMS, Storage data, Locations, file, etc., and also sensitive recorded audio. This malicious app often seems to be a legitimate application that tricks the users into installing them. It is always recommended to download apps from the Google play store and trusted platforms to avoid such attacks in features.
Indicators of Compromise (IOCs)
- 80c0d95fc2d8308d70388c0492d41eb087a20015ce8a7ea566828e4f1b5510d0 – SHA256 Malicious APK
- ab0dbfd4c1edd333d70f5603313dfbd3 – MD5
- 173[.]212.220.230:3617 – IP Address – Malware Communication IP
- hxxps://armaanapp[.]in
- hxxps://pastebin[.]com/VfRCefzG
- hxxps://app1[.]armaan.gov[.]in/armaan_api/v1.5/msg_api/sync.php
- 104.23.98.190.
- 104.23.99.190
- 164.100.60.216
